
Hacker Typing on a Laptop Isolated on Black Background with a Computer Monitor Background Matrix, Digital Data Code in Security Stock Image - Image of crime, hack: 137724075
Premium Photo | Hacker, hacker hacks network, hacker on a dark background. dangerous hooded hacker breaks into government data servers

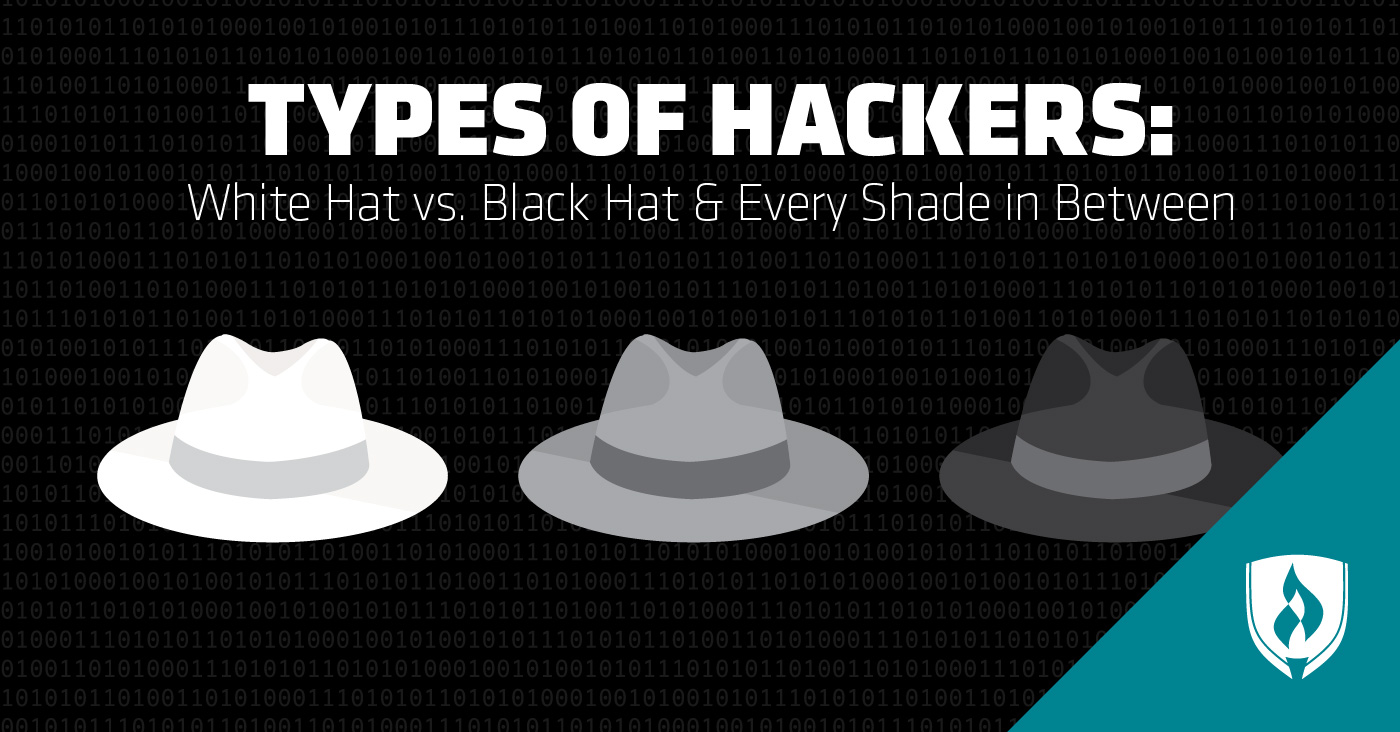
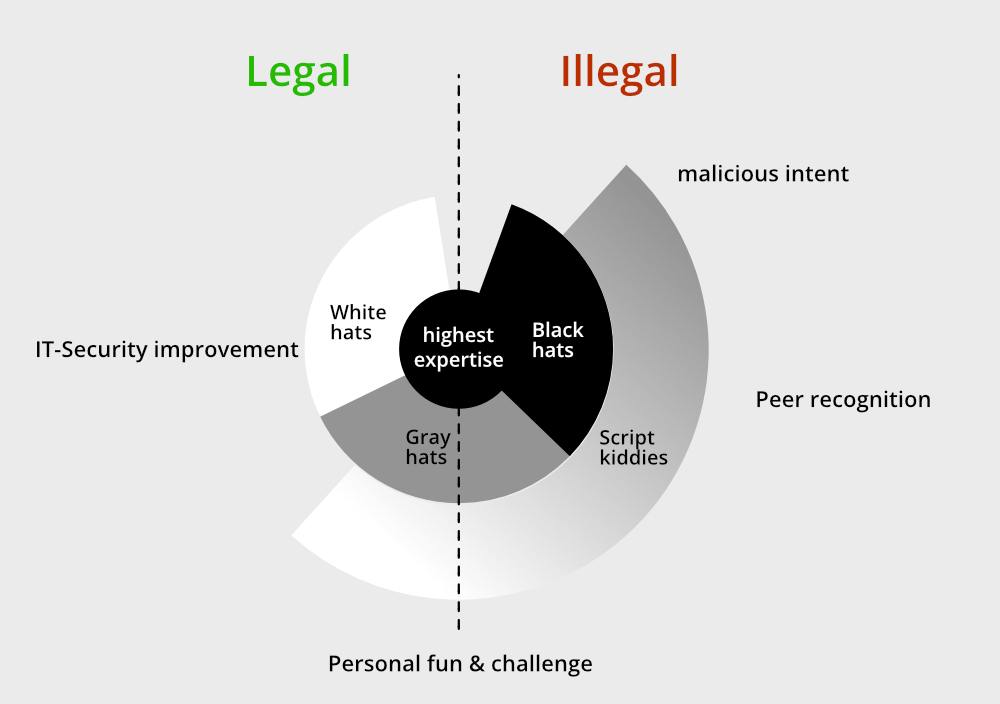
4 Ways to Tell White Hat and Black Hat Hackers Apart (Cyber Security Diploma) - Willis College - Campuses In Ottawa, Winnipeg, Arnprior & Online
















![Best 20+ Hacker Pictures [HD] | Download Free Images on Unsplash Best 20+ Hacker Pictures [HD] | Download Free Images on Unsplash](https://images.unsplash.com/photo-1562860149-691401a306f8?ixlib=rb-4.0.3&ixid=MnwxMjA3fDB8MHxzZWFyY2h8MTF8fGhhY2tlcnxlbnwwfHwwfHw%3D&w=1000&q=80)
